24 October 2023
The $4 Billion Digital Asset Hacking Problem May Finally Have a Solution: Web3SOC

We developed Web3SOC, Security Operations Center to Safeguard Web3 Digital Assets. This systematic framework aims to solve the essential problem in the Web3 security industry, by significantly improving MTTD, MTTR key metrics, attack surface threat modeling, and security maturity for all Web3 digital asset businesses.
None of my old friends in the cybersecurity industry believed it when I presented them our Web3 Risk 2022 Annual Report: the Web3 industry suffered astonishing $4 Billion losses last year.
While at Stanford SBC 2022, the gravity of the situation couldn’t have been clearer. I spoke to dozens of Web3 businesses ranging from DeFi to NFT projects to exchanges and beyond. What I heard was a resounding alarm, each of them was scrambling to take action against the hacks and exploits that have plagued blockchains and Web3 for years. But with most of their security budgets focused on smart contract auditing, monitoring, and blockchain investigation, what else could they do?

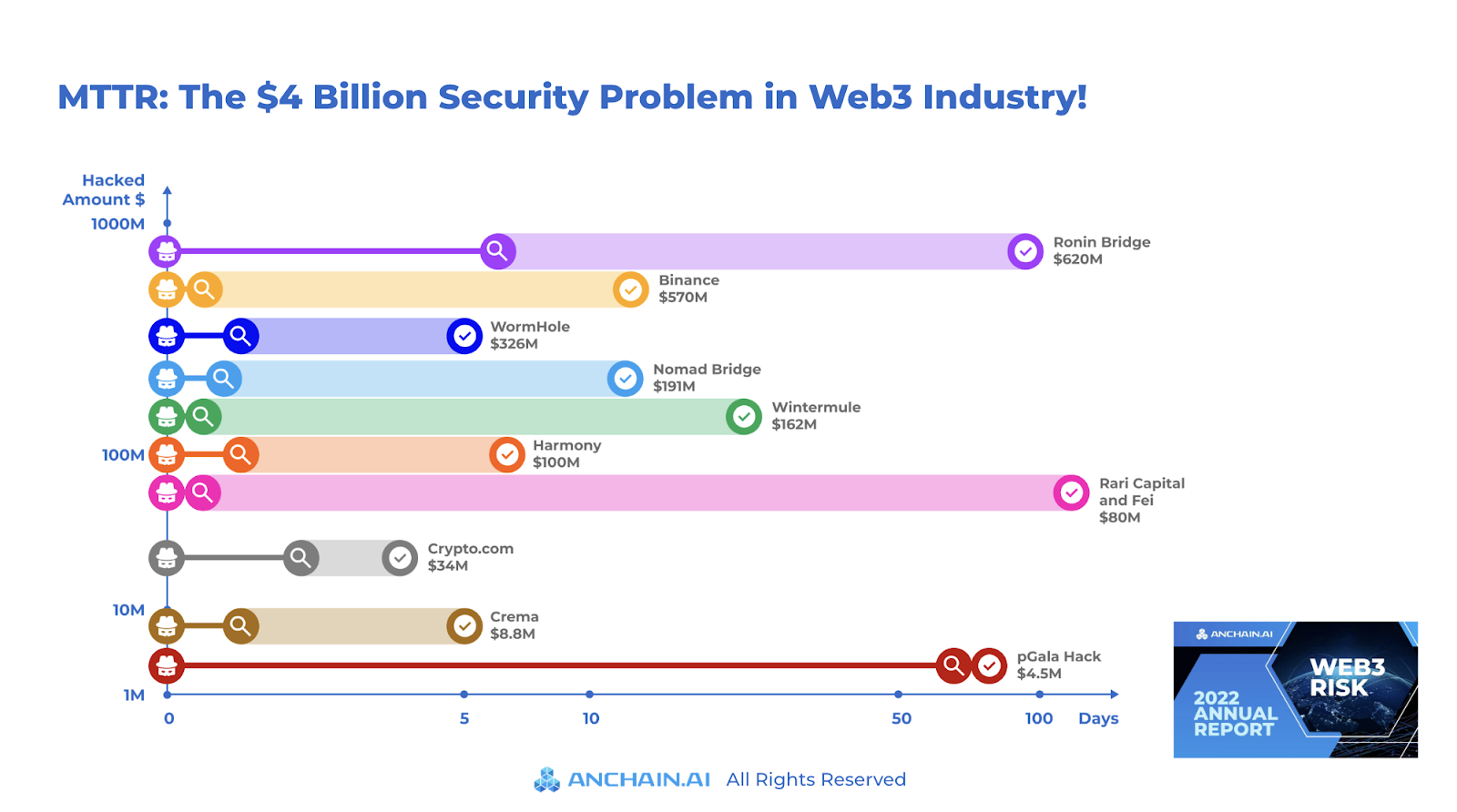
It’s well known that 2022’s biggest hack cost the Ronin blockchain team $620 Million. However, what is rarely discussed is that it took them 5 days to detect (Time to Detect) the hack, and a further 3 months to remediate (Time to Remediate) the vulnerabilities before finally resuming operations.
Metrics from Web3 hacks
Our threat research team analyzed the top Web3 hacks and identified the key metrics that are often considered “cliche” in the cybersecurity industry:
- MTTD: Mean Time To Detect
- MTTR: Mean Time To Respond
- Hacked Amount In Dollar $
Our research reveals several intriguing insights.

Key insight 1: Hacking Web3 is more lucrative than traditional cyber
On average, each major Web3 hack costs $198 Million dollars. Your gut feeling is right, Web3 hacking is lucrative, and many can be traced back to Nation State APT groups.
Key insight 2: MTTD, Mean Time to Detect
The MTTD in Web3 hacks is around 7 days!
In layman’s terms: on average, it takes approximately one week for a Web3 team to realize they have been hacked!
In traditional cybersecurity, the ideal MTTR time is 5 hours or less for best practice.
There is a huge gap to improve the efficiency of human analysts in Web3.
Key insight 3: MTTR, Mean Time to Respond
The MTTR in Web3 hacks is around 30 days! It takes almost ONE MONTH to respond and remediate the hack, including fixing the vulnerabilities in smart contracts, multi-sig, and even Amazon KMS, before resuming normal operation.
To make matters worse, fixing decentralized systems tends to be harder than centralized systems due to the complexity of the attack surfaces, interoperability, openness, transparency, and more.
If more than a month of downtime wasn’t bad enough, such a lengthy MTTR undoubtedly results in a drastically reduced ability to recover stolen funds.

Key Insight 4: The Complex Web3 attack surface.
Why wouldn’t existing SOC / SOAR / SIEM systems seamlessly enable Web3 as they have traditional enterprise?
Web3 has a more complex attack surface than traditional cybersecurity!
Web3 Decentralized Apps are built on top of Blockchains and smart contracts, but we can’t forget that they also rely on Web2:
- Clients such as Metamask wallets
- Front-end code running in the cloud
- Node providers such as Alchemy and Infura
- Oracle and other data providers
Orchestrating a systematic defense of these attack surfaces could be a challenge and requires a new level of security maturity in Web3 teams.
Meet Web3SOC
Web3SOC – Security Operations Center to Safeguard Your Web3 Digital Assets.
For the past 4 years, the AnChain.AI team has been at the forefront of high-profile Web3 incident response, anti-money laundering cryptocurrency tracing, smart contract security auditing, and more. Our team has distilled the extensive experience we’ve gained from the frontlines into our latest innovation aiming to solve one of the core Web3 security problems:
A systematic workflow platform to enable Web3 teams’ human analysts to improve their MTTD and MTTR maturity by 10X, as shown in early pilots.
For instance, at the time of the pGala incident on Binance BNB Pancakes Swap, which was a mirrored token of Ethereum Gala Games token, our EVM event listener detected the transaction in the Mempool, [What is Mempool? ], within a few seconds, not days.
If they had been using Web3SOC, they would have been able to take action and potentially save $4 million dollars and reputational damage!

Unlike traditional SOCs that concentrate primarily on centralized IT infrastructure, Web3SOC is designed to monitor, detect, and collaboratively respond to security incidents across various decentralized systems and platforms, covering the Web3 attack surface.
Build on a strong foundation
Learned from my previous tenure at Mandiant and from other cybersecurity leaders, it’s critical not to try to reinvent the wheel. Our Web3SOC is built on a strong foundation, the 5-step NIST Cybersecurity Framework, extending its support to the Web3 attack surface domain knowledge.

The Web3SOC framework includes 5 core functions:
- Identify: Understand Web3 digital assets, systems, data, and resources that need protection, and develop a comprehensive understanding of the organization’s cybersecurity risk landscape. For example, smart contract auditing fits into this stage.
- Protect: Implement safeguards to ensure critical infrastructure services, prevent or minimize damage from cyber threats, and establish security policies and procedures.
- Detect: Employ monitoring and detection systems to identify cybersecurity events promptly, enabling early detection and effective response. For example, Leveraging machine learning to detect fraudulent actors on Elrond blockchain, and applying Preventative countermeasures such as blocking the transaction falls into this category.
- Respond: Develop and implement an incident response plan to address detected cybersecurity events, minimize damage, and ensure a faster return to normal operations.
- Recover: Restore systems and services affected by a cybersecurity incident by developing a recovery plan, prioritizing critical functions, and incorporating lessons learned to improve overall resilience. For example, the AnChain.AI team traced the $100 Million cryptos for Harmony blockchain fits into this category.
In the next blog, we will do a deep dive into how the AnChain.AI Web3SOC platform could have “prevented” the past Web3 attack, with more details.
Thanks for making it that far, you deserve a freshly minted joke 🍬 by ChatGPT:
“Why did the web3 hacker become an artist?
They found it easier to “draw” from other people’s crypto wallets than their own imagination!”
Join the waitlist for early access to Web3SOC.
Acknowledgments:
Special thanks to my long-time friend, Richard Seiersen who inspired me to measure anything in cybersecurity risks. Kudos to my AnChain.AI team, Philip Werlau, Lina Self, and Reynaldo, for leading the research efforts.